
Security breaches are a common fear of businesses and customers alike. No one wants their data, personal details, or money stolen due to poor website security policies. That’s why a regular website security audit is essential to any business website.
Whether you’ve just built a website for your business or your current website has been ticking along too long without a vulnerability assessment, this guide will take you step by step through the process.
Table of Contents
What is a website security audit?
A website security audit is a full review of your website’s security measures. By assessing everything from third-party integrations to in-house software, you can identify any vulnerabilities in your website’s security.
Website security audits are essential to preventing unauthorized access and breaches. Even if your business is unlikely to be the target of malicious activity, cyber attackers can target any website, large or small.
What are the benefits of website security audits?
We’ve already mentioned the prevention of monetary losses, but that’s not the only benefit of regular website security audits.
- Protect your data: Employee, customer, and financial data can all be the subject of cyberattacks. Auditing your website security helps you protect these against potential breaches – and the subsequent costs.
- Maintain trust: A data breach can be a PR nightmare. With regular audits, you can assure customers, clients, and stakeholders of the security of your website.
- Ensure compliance: Depending on your location or industry, poor website security could lead to penalties or even legal sanctions.
- Improved SEO: Search engines prioritize secure websites.
- Essential maintenance: Website security audits should be on your website maintenance checklist as part of the wider process of running it, helping you spot weaknesses and problems along the way.
How to conduct a website security audit: 7 steps
Whether you’ve never undertaken an audit before, or if you’re just wanting to ensure you follow best practices, it’s worth following these eight steps.
1. Plan your audit
Website security audits are complex and require careful planning if you want to get the most out of them. You need to determine which aspects of your website you will test and how deep the test will penetrate.
For example, you should decide whether to audit only the public-facing side of your website or to include backend systems like the website server as well. Consider whether or not you’ll include third-party integrations and APIs (application programming interfaces) in your audit too.
Tip: Consider stakeholders. When planning your security audit, keep in mind that you may need to present the results to stakeholders. Document everything you use for the audit and everything you assess so that you can provide a comprehensive report..
2. Collect the baseline information
Next, it’s time to gather all the information you have about your website. This might include:
- Domain information, including primary and subdomains.
- Web application details, such as the server and any plugins or extensions used.
- Technology stacks, which might include programming languages, database systems, and content management systems (CMS).
- Third-party applications – this can range from content creation tools to payment gateway apps.
- Hosting provider details.
- Backup procedures, frequency, and locations.
- Error logs and access logs.
- User data, from what type of data is collected to which authentication systems you use for logins or payments.
- Existing security measures and tools are used.
Tip: If the above list looks like it might be a challenge to compile, you should consider using asset discovery tools like SysAid or Jira. These can automate the data collection process and help you find forgotten subdomains or APIs.
3. Research security tools
You don’t have to perform website security audits alone. Security teams can help you perform your audit, as can the huge range of security tools out there, including compliance-focused platforms like Termly, which helps your business address common website policy and consent requirements that factor into data privacy audits.
Consider what your audit needs are, taking into account the size of your website and your industry. Don’t forget to consider what platform you use. Securing a WordPress site requires different tools than those needed for securing a Magento site. This will help you pinpoint what sort of tools you need.
Next, start researching. Make a note of costs, reviews, and any tool’s compatibility with your platform and plugins. You may also want to consider scalability. If your business is going to grow, can the tools you’re using for your audit grow with it?
Tip: Make use of free trials and demos that many security tools offer. That way, you can test out tools during your audit to ensure they meet your needs.
4. Scan and test
Once you know exactly what needs to be audited, it’s time to scan for vulnerabilities. This is typically done using automated software.
There are three types of testing you should perform: manual testing, penetration testing, and stress testing. Here’s how each works for website security audits:
- Manual testing ensures you don’t miss anything not caught using automated tools. You need to review all the code used for your website for potential vulnerabilities. You should also run authentication checks, and checking mechanisms. This is especially important in areas linked to business domain names and third-party tools.
- Penetration testing is usually done using simulated attacks, often by security experts. This is when you attempt to attack or gather data from your website as if you’re a cyberattacker. Penetration testing helps you see how your website performs in real-world scenarios.
- Stress testing, or load testing, is when you evaluate how well your website’s security systems perform when under heavy loads or high traffic.
5. Review access controls
Figuring out who can access your online assets is essential to any website security audit. You should review user access permissions and roles, ensuring they’re properly assigned. Train your team so that everyone uses strong passwords that are regularly changed.
To do this, you should start by documenting all current access controls. For every resource and asset, document who has access and at what level (i.e. read, write, or execute). Then, you should compare these access controls to requirements. Do any users or integrations have access controls beyond what’s required?
Look out for orphaned user accounts of staff who no longer work for your business, third-party tools you no longer use, and any outdated software.
Tip: If your website interacts with Web3 (the decentralized web and blockchains), you should take extra care to review smart contract permissions. Make sure that only actions requiring Web3 smart contracts, like fund transfers, have permission to perform functions on your website.
6. Analyze data transmission
Running a business website requires moving data between various systems. To perform a website security audit, you need to analyze where and when this data is transmitted and pinpoint vulnerabilities.
You should start by mapping out where data is transferred, such as between servers, databases, and third-party apps. You should also classify this data according to its sensitivity. Personal data and financial data are especially sensitive.
Next, make sure data is encrypted during transit. For web applications, HTTPS (SSL/TLS) should be used. Especially sensitive data should be end-to-end encrypted and never travel to locations where it might be leaked.
Tip: There are places outside of your website where data is transmitted, so consider these in your review too. For example, if you get toll-free numbers, or use video calling for customer support lines, ensure any data transmitted is also secure.
7. Report and remediate
Effective website security audits go beyond simply fixing issues as and when you come across them. You should have a replicable process for reporting and remediating any security problems you find.
Start by compiling a detailed report of any vulnerabilities or weaknesses you’ve found. If you need to present your report to stakeholders or clients, make sure the report is easy to understand. Consider using visual tools like heat maps or charts and other visuals.
Next, list security issues in order of priority. Vulnerabilities that could lead to data breaches or unauthorized access should be at the top. Then work through these fixes in order of priority.
When resolving security problems, you may need to involve your third-party vendors in the process. Whether it’s an access issue with remote PC software or questionable user permissions in your security plugins. Communicate with the provider to ensure any potential threats are dealt with.
Tip: When the process is complete, review the process as a whole. Make adjustments and highlight areas needing attention such as server configuration or file permissions, based on any security loopholes found. The website security audit process should be an evolving one that’s regularly reviewed and refined and involves everyone in your business.
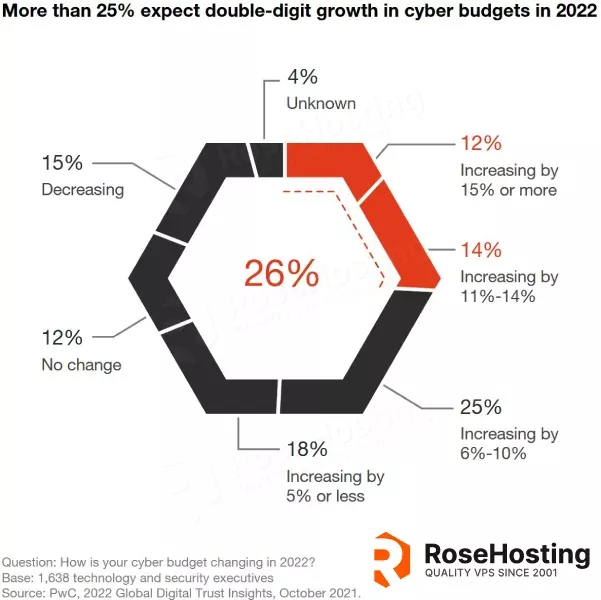
Image from PWC’s 2022 Global Digital Trust Insights
Conclusion: Perfect your security posture with regular audits
Website security audits harness a diverse toolkit of tests and processes, each shedding light on potential vulnerabilities. From automated scans to hands-on penetration tests, every method offers unique insights into how secure your website really is.
The security of your website and digital assets is essential to your business’s safety and legitimacy. Cybercriminals and malware will exploit any vulnerability, but with regular website security audits, you can stay a step ahead.