
An SSH session is like a portal into another machine. If you’re used to working with Windows, you’ll know how easy it is to transfer files from one location to another. Just drag and drop! No text commands, no authentication, none of that.

However, sometimes you will need to download a file from SSH to your local desktop, such as if you are using one of our managed VPS hosting services. And there’s no simple command from within the SSH terminal itself to do this. The two environments are too far apart. However, we have a dedicated tool called “SCP” which stands for “Secure Copy” that’s made for precisely these kinds of situations.
Here’s how it works. First, we have a file on the remote server called filetodownload.txt, as shown here:

We’re going to transfer this file from Linux to our Windows desktop.
Table of Contents
Step 1: Gather the Necessary Information
To transfer a file from a remote server via SSH using SCP, we need the following pieces of information:
- Login credentials – username, server name or IP address, and password
- The port number for SSH connections
- The path to the file on the remote server
- The path to the download location
You should already have the login credentials when you connect to the server using PuTTY, or some other tool, so we won’t go into it here. Learn more about basic PuTTY commands.
As for the port number, you’ll need to know which SSH server port your VPS listens to. It’ll either be 22 (the default port), or it’ll be given to you when you order your VPS from your hosting provider.
To get the full path to the file you want to transfer, enter the “pwd” command on the CLI of the remote server while the file is in your current directory. This will give you the folder name, like this:

Now just append the name of the file to the path you get and you’re done.
As for the path to the download location, that’s something you have to get on your own!
Step 2: Create the SCP Command
The SCP command looks like this:
scp -P [port number] [username]@[server name or IP]:[path to file on server] [path to file on local PC]
Replace the sections in bold with the information you gathered in step 1. For example, the command used for this example is:
scp -P 7022 root@206.196.xxx.xxx:/root/filetodownload.txt C:\Users\[UserName]\Desktop\
Step 3: Running the Command
Open up a command line in Windows. Windows 10 already has SCP installed by default. For this example, we’ll use the Windows PowerShell tool to run the commands. The color contrasts with the yellow, and syntax highlighting is a nice change from the drab command line.
Pasting the above command into the local command line editor gives us:
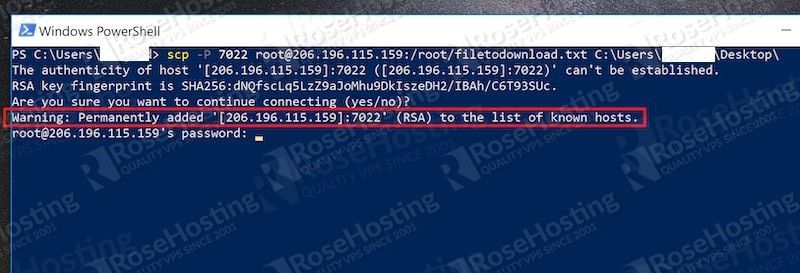
As you can see, you first need to confirm the connection using the RSA fingerprint of the remote server. Once you type “yes”, it’ll be permanently added to the “known_hosts” file.
The “known_hosts” file in Windows is located at:
C:\Users\[UserName]\.ssh\known_hosts
Replace [UserName] with your own Windows username. It’s a file without an extension, like this:
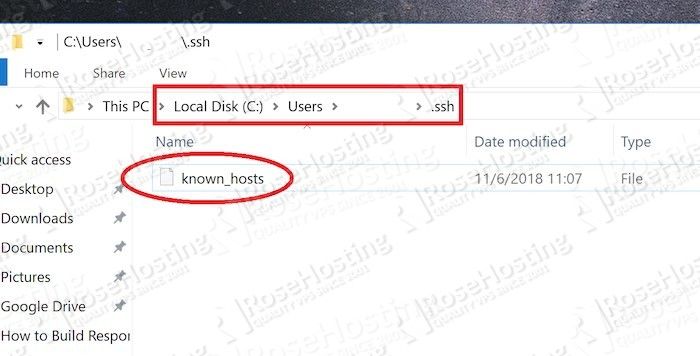
An editor like Notepad++ is ideal for these kinds of files. Each RSA fingerprint is added on a new line. This allows you to clear them easily by deleting an entire line at once if you ever need to remove an entry.
Once you provide your password in the prompt, the file is downloaded immediately, as shown here:
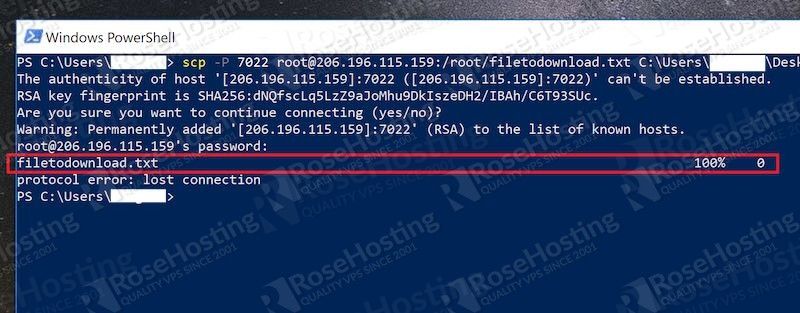
And you’re done! Navigate to the location you specified in your SCP command and the file should be visible.

SCP is the most direct way to transfer and download files from remote servers to local systems. It makes use of the same SSH protocols, so the connection is encrypted all the way through, making it immune to man-in-the-middle attacks. Hopefully, this tutorial will help you use it in an efficient, and easy manner. If you use one of our Managed Linux VPS services, and you have an issue with SCP or need more information about it please don’t hesitate to contact our 24×7 Linux Server Support, which comes included with your hosting plan.
If this tutorial helped you move files from your remote server to your local machine, maybe consider sharing this knowledge with your friends by using our share shortcuts. You can also leave any additional tips or questions in our comment section below. Thank you.